Understanding Google Pay: The Evolution of Seamless Digital Payments
What began as "Pay with Google," a forward-thinking initiative launched by Google, has seamlessly evolved into Google Pay, the unified digital payment platform we widely use today. Back in May 2017, Google introduced its Google Payment API, exciting users with a promise of significantly simplifying the online checkout experience for consumers. Initially, these powerful tools were exclusive to beta program participants, allowing select merchants to offer a much smoother way for customers to input their payment details during purchases. Now, this convenience is universal, extended to a vast network of online retailers.
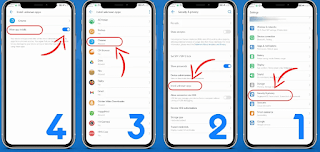
Google officially launched "Pay with Google" to streamline payment processes across Android devices and a rapidly growing number of e-commerce businesses online. This new payment technology effortlessly simplifies shopping and payments for various services and subscriptions through a few easy steps. The innovative service wasn't confined to mobile; it was also integrated with the Google Chrome browser on desktop devices. Consumers benefit from a streamlined payment method that provides automatic filling of required data and shipping information, making purchases possible with just a few clicks.
In its early stages, "Pay with Google" first rolled out in the United States, Brazil, and the United Kingdom, partnering with major platforms such as Airbnb, Deliveroo, Instacart, Kayak, Fancy, HotelTonight, StubHub, JustEat, and Papa John's. This service marked a significant departure from Android Pay. While Android Pay required companies to integrate the application within their own apps, "Pay with Google" was inherently designed for automatic, seamless, and time-saving transactions, offering a smoother user experience.
Today, Google Pay stands as the complete realization of that vision. It’s a unified platform that combines the best of both "Pay with Google" and the original Android Pay, offering a consistent and convenient way to pay online, in apps, and in physical stores. This platform automatically handles time-consuming payment and shipping details, ensuring a hassle-free and swift checkout process. Looking ahead, Google continues to push boundaries, with ambitions to enable peer-to-peer money transfers via voice commands, a feature that has already seen significant development through integrations with Google Assistant.
In essence, Google Pay has matured into an indispensable tool for modern commerce, providing a fast, secure, and user-friendly method for managing digital transactions across the globe.